Did you know hackers can exploit 125 weaponized vulnerabilities in VPN products to attack their targets?
Virtual Private Networks (VPNs) are widely used solutions that allow users to establish a secure encrypted connection with the internet, allowing them to work from anywhere in a secure manner. The usage of VPNs saw a surge, especially during the pandemic when the world’s workforce was working remotely.
When this “secure” connection is compromised, it allows threat actors to access secluded networks, perform data exfiltration, and install payloads and other sophisticated tools, resulting in ransomware attacks.
|
Popular VPN breaches |
|
 |
|
In 2020, our researchers investigated eight popular vendors and found 147 vulnerabilities in VPN products. This year, we have broadened our scope to investigate 71 vendors and the vulnerabilities that exist within their products.
Top 5 Findings
-
Our analysis of 430 unique VPN products offered by 71 vendors identified 1,281 vulnerabilities across them.
-
Attackers have already weaponized 10% of these vulnerabilities.
-
APT groups have associations with nine of these vulnerabilities, and ransomware groups have the means to exploit eight of them. Notable names are APT 29, APT 33, and Fox Kitten APT groups, and Conti, REvil, LockBit, and Pay2Key ransomware groups.
-
CISA’s Known Exploited Vulnerabilities (KEV) catalog lists 2.4% of these vulnerabilities.
-
Popular scanners such as Nessus, Nexpose, and Qualys are not detecting 23% of the vulnerabilities in VPNs.
This blog explores the findings from our research into VPN vulnerabilities.
Vulnerability Prioritization
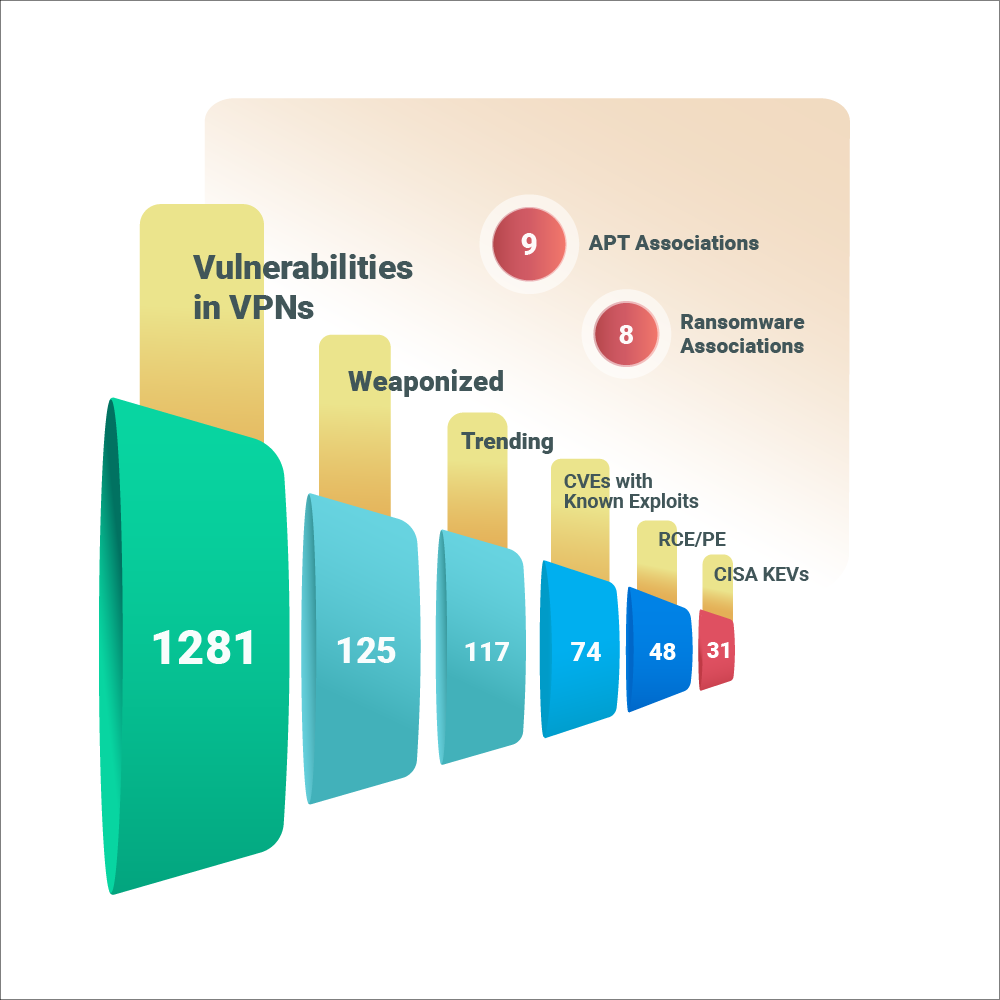
Our investigation brought to the forefront 1,281 vulnerabilities in 430 unique VPN products.
Today, attackers are not only developing sophisticated techniques to exploit networks but are also willing to share the knowledge with their counterparts. This being the case, a vulnerability, once weaponized, becomes a permanent open attack vector that attackers can exploit whenever they choose to.
Our research shows that the weaponized vulnerabilities are ripe for exploitation. Notably, 117 VPN vulnerabilities are trending in the deep and dark web, which is a sure sign that attackers are constantly tracking exposed assets for these vulnerabilities.
APT and Ransomware Associations: Of particular concern are 12 vulnerabilities that have associations with APT or ransomware groups, with 5 of these having both associations. These vulnerabilities are particularly dangerous owing to the magnitude of the impact caused when exploited. From data theft to sensitive data leaks and data encryption to ransom demands, the stakes are high, affecting brand reputation and business continuity.
Let us look at the vulnerabilities with both APT and ransomware associations.
|
CVE |
APT Associations |
Ransomware Associations |
Vendor |
Affected Products |
|---|---|---|---|---|
|
CVE-2019-11510 |
7 |
7 |
Pulse Secure |
37 |
|
CVE-2019-11539 |
2 |
2 |
Pulse Secure |
135 |
|
CVE-2020-5902 |
3 |
2 |
F5 |
84 |
|
CVE-2018-13379 |
9 |
5 |
Fortinet |
2 |
|
CVE-2019-1579 |
5 |
1 |
Palo Alto |
3 |
The Fox Kitten APT group has exploit methods for all the above-mentioned vulnerabilities that exist in popular VPNs such as Pulse Secure, F5, Fortinet and Palo Alto, while the Pay2Key ransomware group is associated with four. Other noteworthy threat groups are the APT 29 and APT33, and the notorious Conti and REvil ransomware players.
A notable callout is CVE-2018-13379 in FortiOS, targeted by nine APT groups and five ransomware groups. This CVE is also a part of CISA KEVs. An attacker who exploits this vulnerability can download system files via specially crafted HTTP requests without authentication.
Organizations must pay attention to these vulnerabilities and ensure they are remediated immediately lest their VPNs are used as entry points for claiming a strong foothold on target networks.
Analyses of Severity Ratings
Critical and high severity vulnerabilities are deemed severe as they can be highly impactful if exploited, thus warranting immediate attention. Of the VPN vulnerabilities, 57.5% fall under this category.
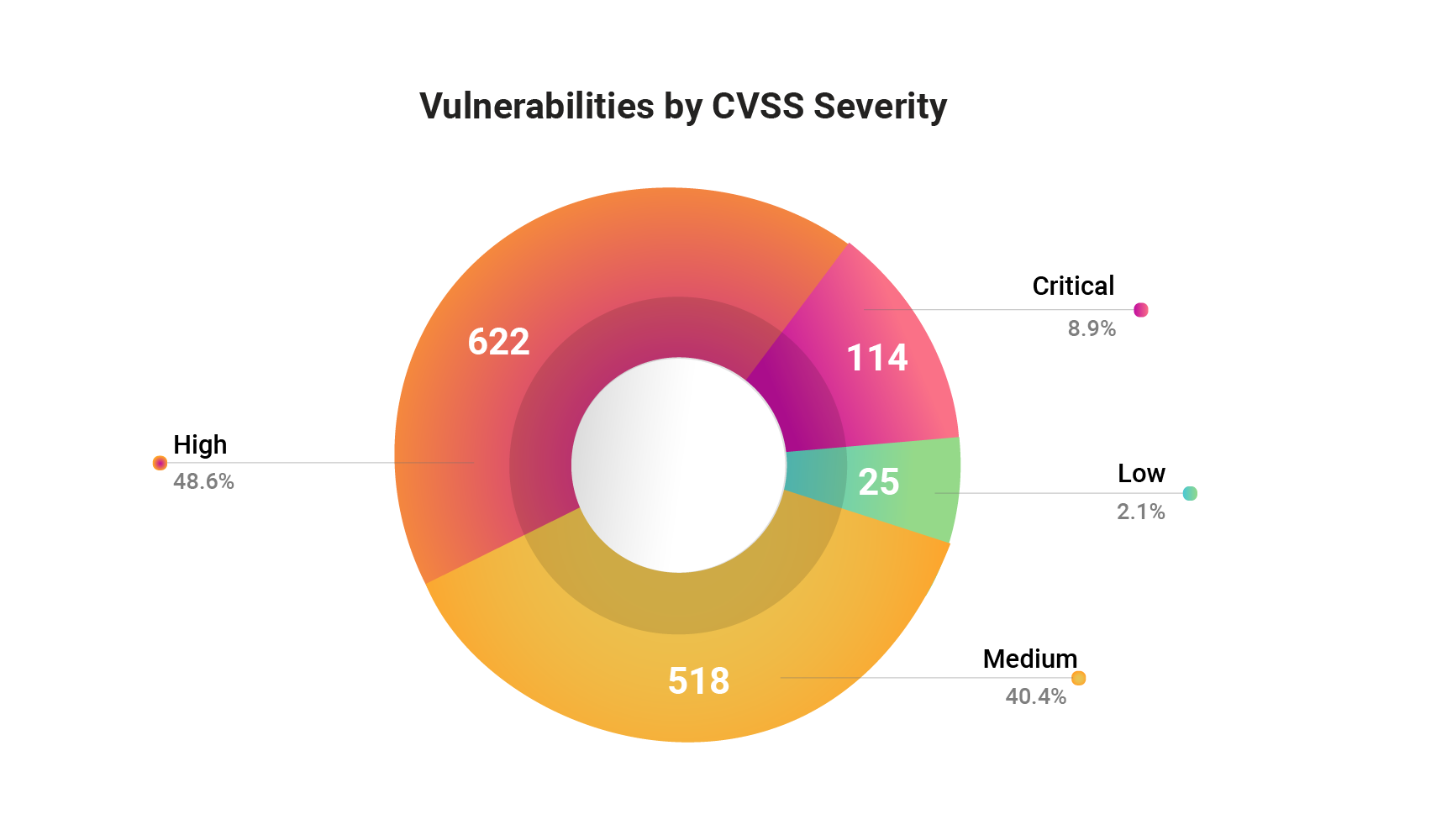
While the count of critical and high severity vulnerabilities is overpowering, we should not forget that low and medium severity ones are dangerous too. These are attackers’ trump cards, as they mostly go unnoticed in the flurry of vulnerabilities to be patched. After all, a single unguarded vulnerability, however inconsequential as it might seem, is sufficient for attackers to dig their way through vulnerable networks.
We highlight four medium severity vulnerabilities with APT and ransomware associations and CISA’s warning, reiterating the above. Our score assigns a higher rating to these vulnerabilities, reflecting their threat context and exploit impact.
|
CVE |
Vendor |
NVD’s Score |
Securin’s Score (on 10) |
Securin’s Rating |
|---|---|---|---|---|
|
CVE-2017-12319 |
Cisco |
5.9 (medium) |
7.23 |
High |
|
CVE-2018-13383 |
Fortinet |
6.5 (medium) |
8.34 |
High |
|
CVE-2019-11507 |
Pulse Secure |
6.1 (medium) |
8.1 |
High |
|
CVE-2020-8195 |
Citrix |
6.5 (medium) |
7.73 |
High |
Latency Analysis
One of the key findings from this research is that attackers are taking advantage of the NVD latency by weaponizing vulnerabilities even before anyone knows their existence. Since they are not on the NVD, the scanners will not be picking these vulnerabilities, giving attackers a free pass to exploit and breach.
-
Of the 74 CVEs with known exploits, 48 (65%) were exploited before publication in the NVD.
-
Threat actors targeted eight CVEs with exploits published before they were added to the NVD.
This means that 65% of the vulnerabilities were exploited even before organizations were made aware of the presence of the vulnerability. How can organizations protect themselves against threats that they do not know exist?
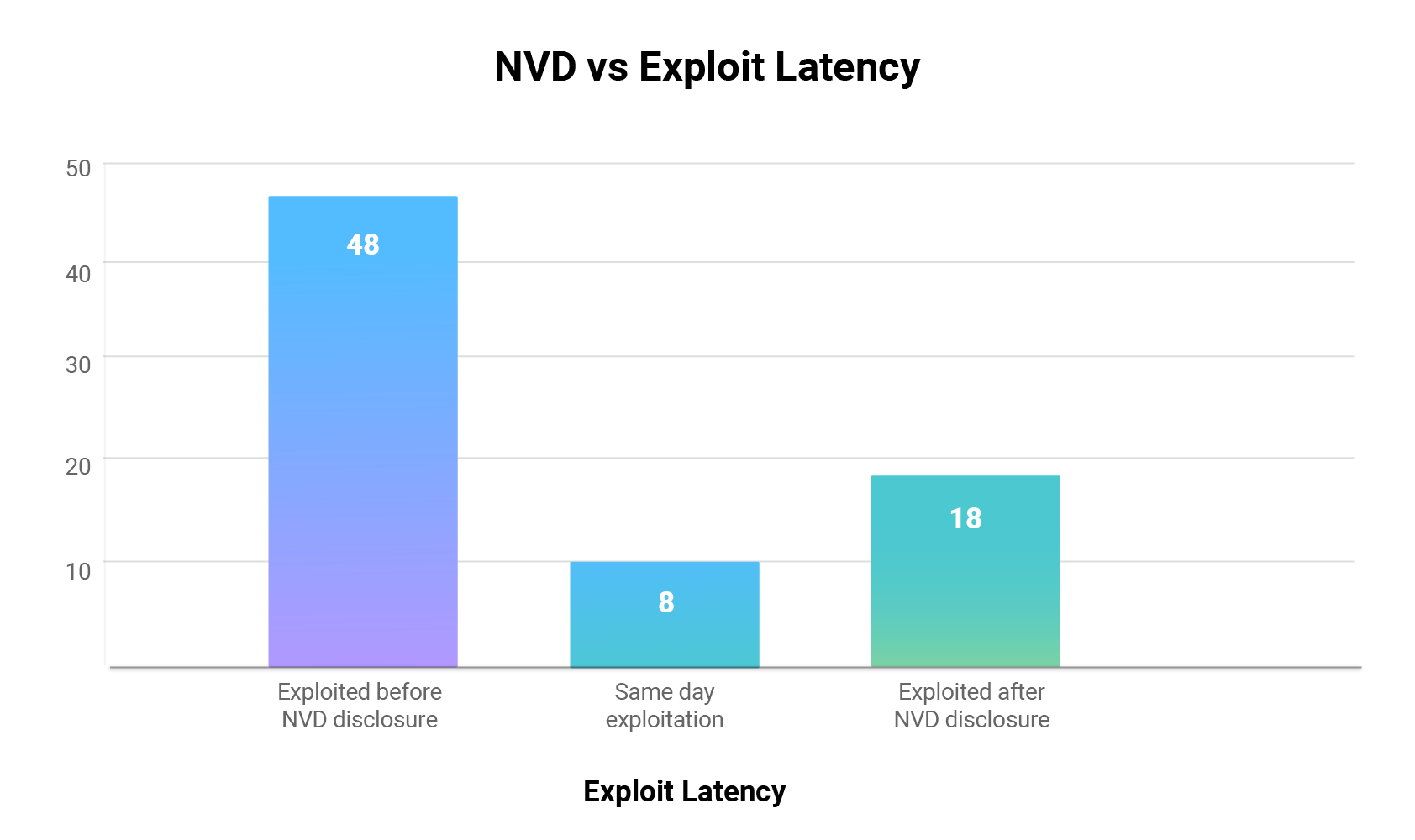
Another noteworthy observation is that five of the vulnerabilities in VPNs were weaponized before a patch could be released for them. This falls under the most dangerous scenario where attackers exploit vulnerabilities that do not have official fixes.
The workaround for this problem is to predict vulnerabilities that hackers find easy to weaponize. Securin’s threat intelligence platform VI uses predictive AI and ML models to predict the probability of weaponization. This data allows us to warn our customers early in the game.
Vulnerabilities on Attackers’ Radar
Vulnerabilities with a high likelihood of exploitation: Our early warning predictive analytics assesses vulnerabilities from an attacker’s mindset. Based on hacker chatter and activities on the internet, our researchers have highlighted 18.2% of the identified vulnerabilities as having the highest chances of exploitation.
Our analysis also points to 11 vulnerabilities with a high likelihood of exploitation that could soon reach the warning threshold. Organizations must closely watch this subset, as attackers are weaponizing vulnerabilities at an alarming pace today.
We highlight the top 10 weaponized VPN vulnerabilities prioritized by our researchers.
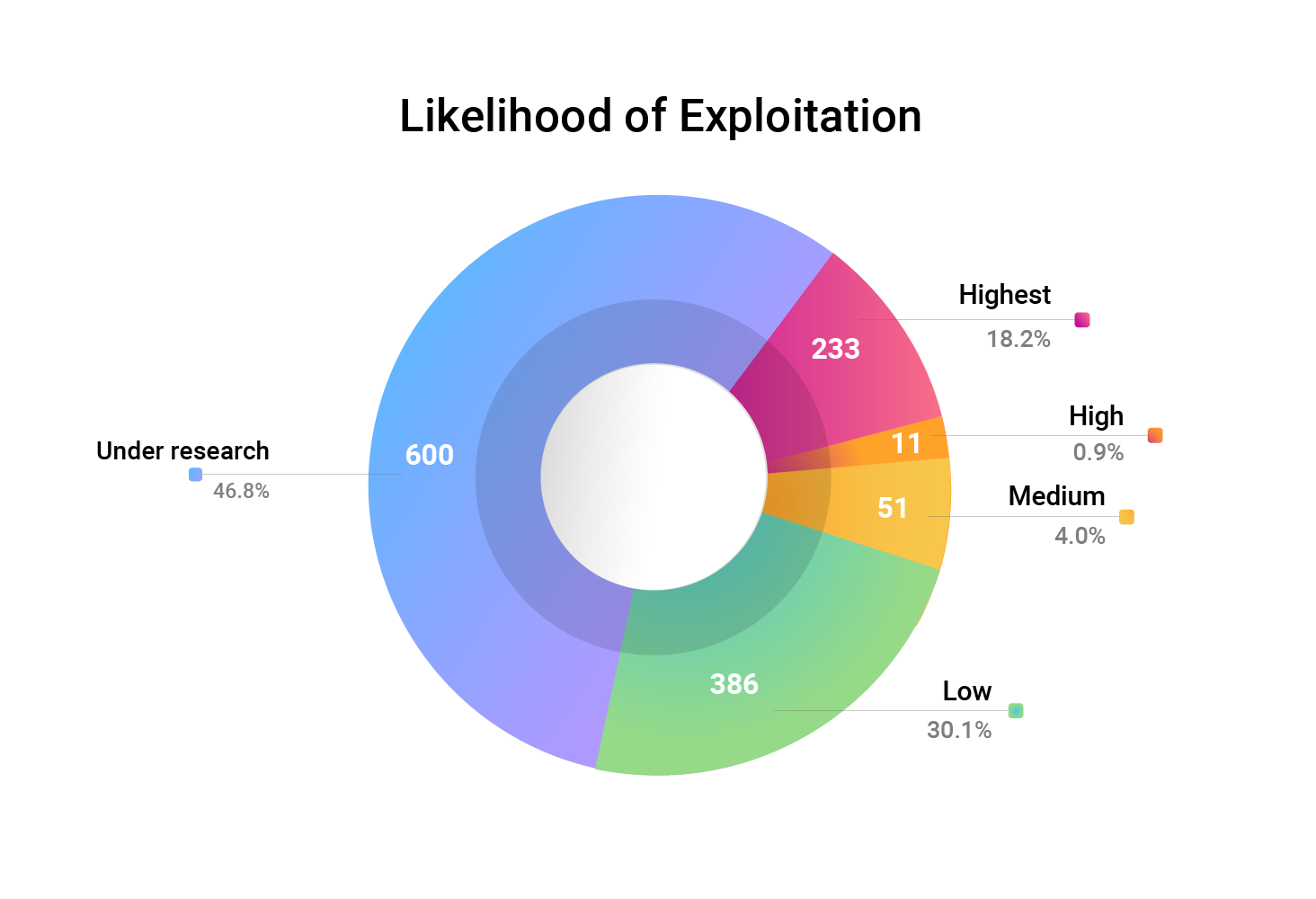
Vulnerabilities that could soon be weaponized: It is also interesting to note that 157 of the vulnerabilities are yet to be weaponized, have no known exploits, and get the highest exploitability rating in our platform. These vulnerabilities are usually not prioritized for patching, as they do not signify any danger at first glance. However, attackers are scouting VPN distributions worldwide for these 157 unique entry points, waiting for a chance to pounce on any unpatched instance.
Note: Securin researchers will continue to investigate these vulnerabilities and provide warnings as soon as they are weaponized.
We highlight the top 10 yet-to-be weaponized vulnerabilities to watch out for:
Top Vendors and Products
What are the VPN products you use that could put you in danger? Here are our product insights.
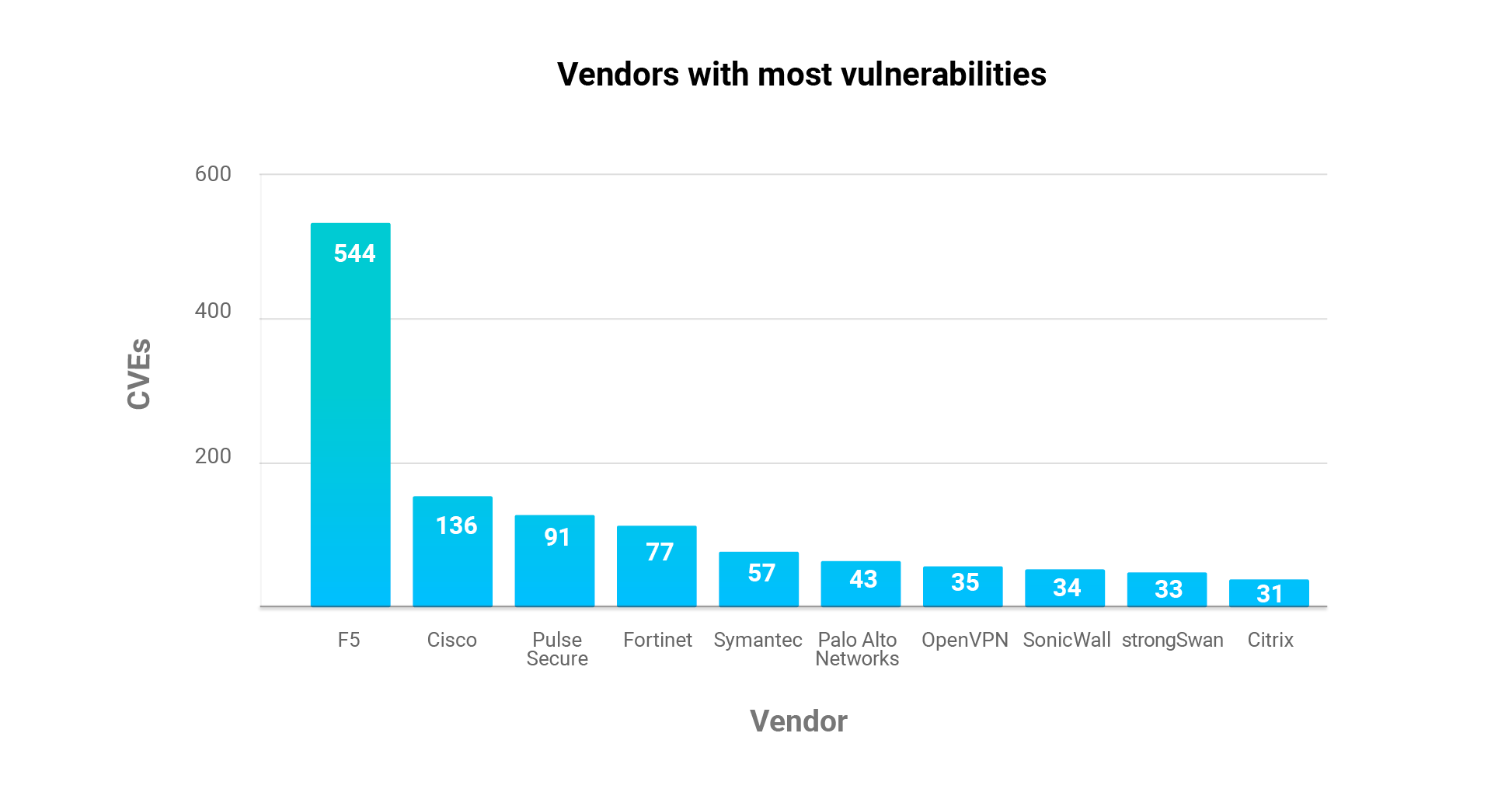
Top Vendors: F5 accounts for 42.8% of all CVEs collected, with Cisco (10.7%) and Pulse Secure (7.15%) coming at a distant second and third. Further, F5, Cisco, Symantec, and Pulse Secure are the vendors with the most weaponized vulnerabilities and RCE/PE exploits.
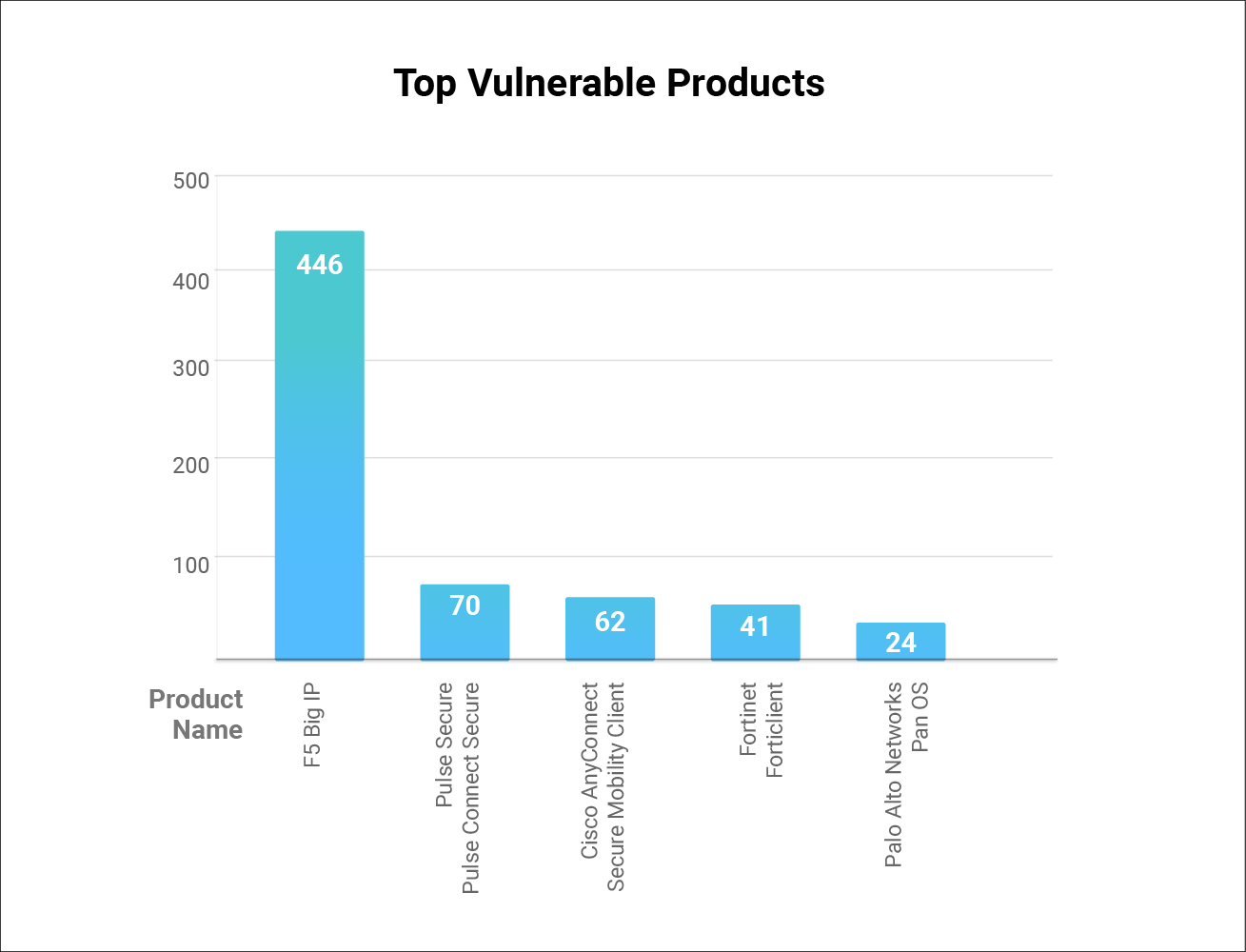
Top Products: F5 takes the cake here as well with 446 vulnerabilities in its Big IP product. Pulse Connect Secure from Pulse Secure and Cisco’s AnyConnect are the next two on the list.
Exposure Analysis: Here is a look at the VPN products that have the most exposure on the internet, according to Shodan’s search results.
|
Products |
Exposure Instances |
Total Number of Vulnerabilities |
|---|---|---|
|
SonicWall SSL-VPN |
1,313,480 |
34 |
|
F5 Big-IP |
1,828 |
446 |
|
Fortinet FortiClient |
7,003 |
44 |
|
Cisco AnyConnect |
179 |
62 |
|
Pulse Secure Pulse Connect Secure |
24 |
70 |
When high availability (exposure) meets high access points (vulnerability count), attackers have a golden opportunity.
CVSS Distribution across Vendors: Our examination of the vulnerabilities across top affected VPNs brought up an interesting finding: high and medium severity vulnerabilities dominate their exposures!
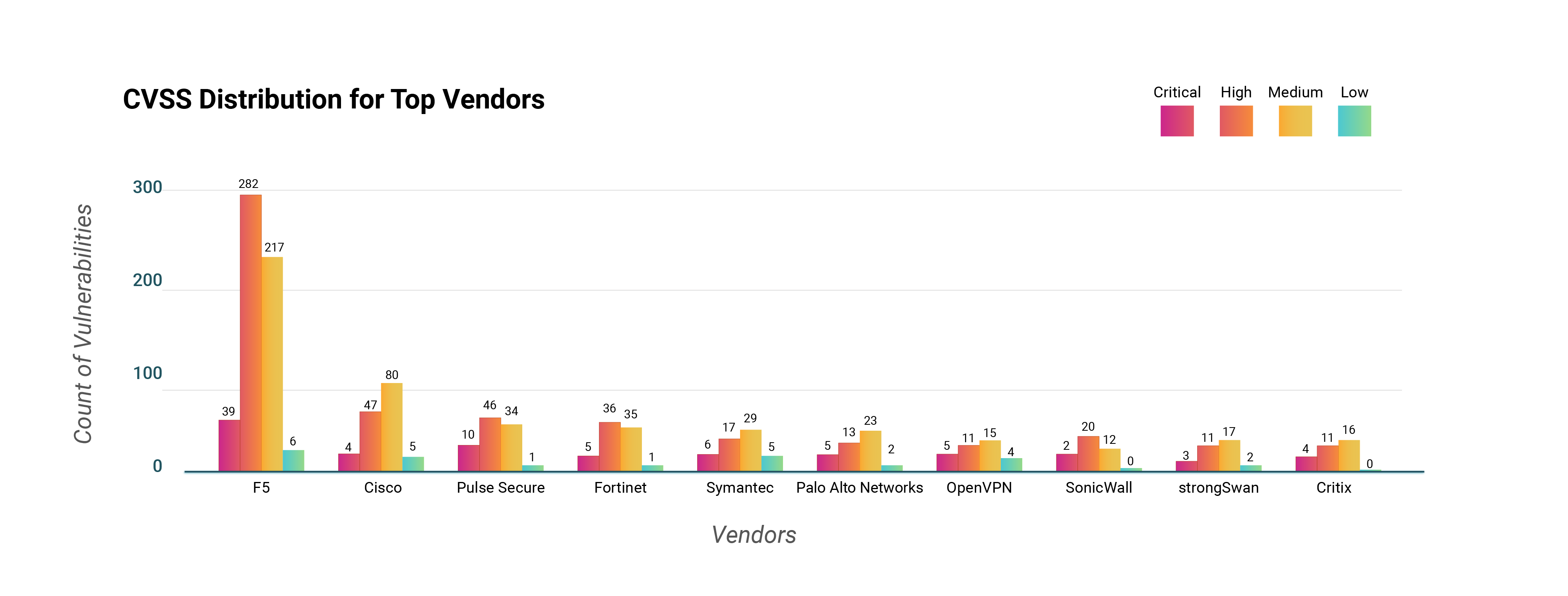
While it is important to address critical vulnerabilities due to their highly impactful nature, organizations would be at a loss if they ignore the high and medium severity vulnerabilities. An approach that adopts a risk perspective considering factors like ransomware and APT associations, trending factors, exploitability, the likelihood of exploitation, and CVSS severity, amongst others, will enable organizations to thwart the threats that matter to them proactively. Context is key!
A worrying aspect of this year’s study was that most of the vendors under the lens showed an increase in the overall count of vulnerabilities in their VPN offerings.
|
Vendor |
2020* |
2022* |
||
|
Vulnerabilities |
Weaponized Vulnerabilities |
Vulnerabilities |
Weaponized Vulnerabilities |
|
|
Pulse Secure |
44 |
3 |
89 |
14 |
|
Cisco |
44 |
4 |
136 |
19 |
|
Fortinet |
30 |
9 |
77 |
11 |
|
OpenVPN |
27 |
5 |
35 |
4 |
|
SonicWall |
9 |
6 |
34 |
6 |
|
Citrix |
16 |
1 |
31 |
5 |
|
Palo Alto |
1 |
1 |
43 |
2 |
*In 2020, we investigated 8 vendors and 147 vulnerabilities overall. The 2022 research studied 1281 vulnerabilities across 71 vendors.
While F5 did not have a significant impact in our previous report, vulnerabilities in its VPNs in this year’s study outnumber the rest. In contrast with our research in 2020, the researched vulnerabilities have grown from 147 to 1,281; correspondingly, the count of vulnerabilities in VPNs from top vendors such as Pulse Secure, Cisco, Fortinet, SonicWall, and Citrix has more than doubled.
With over 70 vulnerabilities being added to the NVD in a single day in 2022, this increase in identified vulnerabilities is not surprising. The more crucial aspect is that today’s security cycle stands apart from the development cycle, leading to this issue.
Vendors must focus on merging the security cycle with the development cycle to ensure weaknesses that could give rise to vulnerabilities are addressed right at inception. Secure code should become the norm.
What are the weaknesses causing vulnerabilities in VPNs?
We observed a total of 117 weaknesses in code, giving rise to the 1,281 vulnerabilities identified in our study. Prominent amongst these are CWE-79 and CWE-20 ranked second and fourth dangerous weaknesses, respectively, by MITRE. These are commonly occurring weaknesses that result from improper handling or validation of input parameters.
Interestingly, CWE-200 (Exposure of Sensitive Information to an Unauthorized Actor), CWE-269 (Improper Privilege Management), and CWE-427 (Uncontrolled Search Path Element) take the spots #7, #8, and #10 in the Top 10 VPN CWEs. However, these fall outside the MITRE 2022 Top 25 CWEs (#33, #29, and #27, respectively). This signifies that you need to look beyond the top MITRE weaknesses to address the root cause of vulnerabilities.
Our research into MITRE mapping for CISA KEVs highlights the challenges we encountered while performing the mapping exercise, the gaps in predominant sources today, and how we overcame them to complete the exercise. Click here to know more about our research.
Techniques and Tactics
To understand how attackers could exploit the vulnerabilities in VPNs, we mapped the CVEs to their MITRE techniques and tactics.
-
Unsurprisingly, the top three tactics were Initial Access, Impact, and Execution.
-
CVE-2022-1388 stood apart as it could be used in six different ways in an attack: Initial Access, Persistence, Privilege Escalation, Defense Evasion, Lateral Movement, and Impact. This vulnerability in BIG-IP systems could allow unauthenticated attackers to execute arbitrary system commands and disable services. The impact combined with the capabilities make CVE-2022-1388 a highly dangerous vulnerability that must be patched without delay.
Are Scanners Finding It All?
The go-to solution for organizations to identify vulnerabilities in their systems is to use a scanner. We cross-referenced the identified vulnerabilities with popular scanners’ results to understand if they were flagging all.
-
A staggering 294 vulnerabilities in VPNs are not being detected by popular scanners such as Nessus, Nexpose, and Qualys. This means that these vulnerabilities will not be detected even if they are in your systems.
-
32 of the missed vulnerabilities have been weaponized.
-
CVE-2021-27860 (FatPipe VPN RCE) and CVE-2020-9054 (Zyxel Firmware RCE) are CISA KEVs with elapsed deadlines of Jan. 24 and Apr. 15, respectively, when they should have been patched as directed by the federal mandate. These do not have scanner plugins.
If the scanners you use do not catch these vulnerabilities, you will miss out on their patches and create a pathway for attackers to exploit.
Weaponized Vulnerabilities in VPNs missed by scanners
Five Things Organizations Can Do to Safeguard Their Networks
Organizations that deploy VPNs need to adopt rigorous cybersecurity practices to manage the vulnerabilities present in them. Despite the dangers unearthed by this study, the most surprising fact is that all VPN vulnerabilities have patches available. However, there still exist multiple VPN installations exposed to actors with malicious motives.
What can organizations do to safeguard their networks? Here is what we recommend:
-
Adopt a regular attack surface management to discover the vulnerabilities exposing your network.
-
Look beyond just direct VPN deployments and consider all assets for any indirect communication with exposed VPNs.
-
Monitor the overall organizational asset ecosystem to ensure no other attack vector, like incorrectly configured assets, is allowed to link to the VPN vulnerabilities, allowing for an attack chain that could end in a total organizational network compromise.
-
Rigorously adopt the mitigations suggested by vendors of the VPNs you use.
-
Practice patching high-impactful vulnerabilities as an ad hoc, on-demand process, based on the threat context, rather than waiting for a sprint cycle. By this time, there are chances that your network might have already been infiltrated.









