Red Teaming Assessment
CSW's Red Teaming service involves launching a simulated, goal-oriented, and stealth-based attack on an organization to test the efficacy of their security controls and verify their ability to identify, contain, and eradicate threats. Our red team mimics a real-world attacker’s strategies and aims to compromise the organization without being detected by any security protocols.
An Overview:
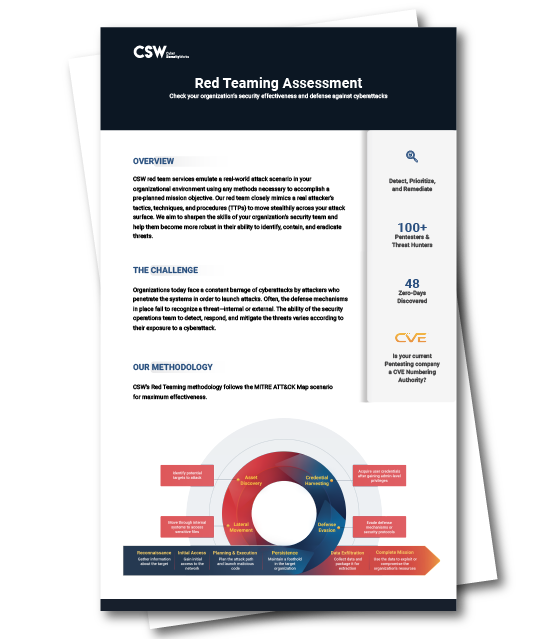
CSW’s Red Teaming methodology follows the MITRE ATT&CK Map scenario for maximum effectiveness.
Our Methodology:
- Plan and launch the attack with special commands used by attackers
- Evade any encountered defense mechanism or security protocols
- Acquire user credentials after gaining admin-level privileged access
- Identify sensitive files, networks, servers, and directories
- Move laterally through the company systems to access sensitive files
- Collect sensitive data and package it for extraction
- Use the collected data to compromise the organization’s resources