Resources
Get the latest updates from our cybersecurity resources: White Papers, Data Sheets, Case Studies, Solution Briefs, and more.

.png)
Ransomware Index Update Q2 & Q3 2022
The 2022 Index Update Q2 & Q3 report tracks the vulnerabilities that facilitate Ransomware attacks and delves deep into their MITRE ATT&CK tactics and techniques. The report also provides interesting observations about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022 and top ransomware vulnerabiltiies that could be exploited in the near future.
.png)
CSW Helps DreamSpring Migrate to AWS and Halve Hosting Costs
DreamSpring, a nonprofit community lender dedicated to eliminating systemic wealth inequities, partnered with CSW to migrate its lending platform to the Amazon Web Services (AWS) cloud computing platform.
Ransomware Index Update Q1 2022
Ransomware Index Update for Q1 2022 dives deep into the latest developments in ransomware attack arsenal, and the gaps in data intelligence that act as a roadblock in organizations’ security journey.
.png)
AWS Cloud Security Assessment
CSW’s Cloud Security Assessment is designed to help you protect and optimize information, systems, data, and other assets hosted on AWS.
AWS Security as a Service
With our AWS Security as a Service offering, CSW becomes an extended member of your security team by continuously monitoring and assessing your AWS infrastructure.

AWS Cloud Security Management
CSW’s Cloud Security Management services are designed to continuously reduce your overall cloud attack surface by looking at your vulnerabilities across your entire technology stack.
SaaS Security Assessment
CSW's security assessment of Software-as-a-Service (SaaS) audits the software delivery model and resilience of the entire SaaS platform and all technology stacks involved—application, storage, and underlying infrastructure. We conduct a thorough analysis to help organizations remediate vulnerabilities that could compromise their SaaS platform.

API Penetration Testing
CSW’s API penetration test validates the security of your organizational methods and corresponding data ensuring that the transfer of information from web or mobile applications to other databases or systems can be safely carried out. Our testing methodology uses standardized processes to ensure consistency and ensure your API workflow is secure. We evaluate all applications based on OWASP API Top 10 and CWE Top 25 programming errors.
.png)
Ransomware Spotlight Report 2022
The 2022 Spotlight report provides a deep insight into vulnerabilities that facilitate Ransomware attacks. Learn more about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022.
Ransomware Index Update Q3 2021
Ransomware Index Update for Q3 provides the latest ransomware trends, and the new groups, vulnerabilities and weaknesses tied to ransomware. Understand what vulnerabilities offer the greatest threat and stay protected.
Web Application Penetration Testing
CSW’s web application penetration test provides a comprehensive understanding of how user inputs change data inside an application. Our proprietary framework helps to discover multiple attack vectors including thorough and dynamic testing of user, network and API interfaces.
Network Penetration Testing
CSW’s network penetration testing program provides clarity on critical vulnerabilities, helps organizations stay ahead of the attacker, aids in building a resilient security program to defend against advanced persistent threats (APTs) as well as attacker behavior, including tactics, techniques and procedures (TTPs) and assists you in maintaining a robust brand reputation.
Mobile Application Penetration Testing
The increasing demand for mobile applications worldwide multiplies the risk of a breach, especially when vulnerable applications are used to access sensitive data. CSW’s experienced penetration testers look for vulnerabilities in data storage, network communications (API), source codes, and security configurations during this engagement.
Internal Network Penetration Testing
We provide our clients with an accurate picture of the risk associated with their internally facing assets. Our Internal Network Penetration testing service is designed to test the effectiveness of an organization’s security controls towards preventing attackers from pivoting and moving laterally through your company’s infrastructure.
External Network Penetration Testing
We help our clients improve their security posture by providing guidance as to which weaknesses present the most risk to the business. This allows organizations to make more efficient use of their very limited resources by focusing on the most important issues.

Red Teaming Assessment
CSW's Red Teaming services emulate a real-world attack scenario in your organizational environment using any methods necessary to accomplish a pre-planned mission objective. Our red team closely mimics a real attacker’s tactics, techniques, and procedures (TTPs) to move stealthily across your attack surface.

Vulnerability Management as a Service
CSW’s security analysts will help you gain 360-degree visibility of your security exposure and help you remediate vulnerabilities that exist within your network.
How CSW Helped a Debt Recovery and Portfolio Management Company
Read about how CSW conducted a Red Teaming exercise on a leading American debt recovery and portfolio management company and helped them gain cyber resilience.
Ransomware Index Update Q2 2021
Ransomware index update for Q2 looks at new vulnerabilities tied to ransomware, new exploits, APT Groups, and Ransomware families. Build resilience to defend your ecosystem from crippling ransomware attacks.
Ransomware Index Update Q1 2021
Ransomware index update for Q1 2021 brings new vulnerabilities, exploits, APT Groups and Ransomware families that have become active in the first quarter of 2021. Get updated insights about this evolving threat and know your exposure to it.

Our Services & Solutions
CSW offers services such as Vulnerability Management as a Service (VMaaS), Penetration Testing (Network, Mobile, Cloud, SaaS, Web etc) and compliance services such as PCI ASV & DSS to improve your security posture and strengthen your defenses.
Ransomware 2021 Spotlight Report: Threat and Vulnerability Management
From APT groups, ransomware-as-a-service, targeted products and preferred weaknesses, this report delves deep into every aspect of ransomware and presents extensive insights and actionable information.
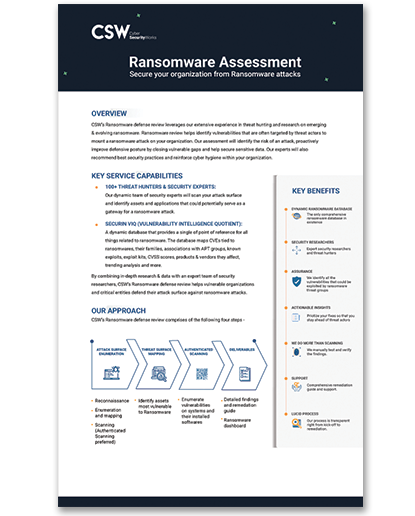
Ransomware Exposure Assessment
Ransomware Exposure Assessment helps identify vulnerabilities that are often targeted by threat actors to mount a ransomware attack on your organization.

Penetrating Testing Datasheet
Our penetration testing simulates a real-world attack on digital assets. We adopt a hacker’s perspective to detect and exploit vulnerabilities in an organization’s environment to determine if we can move laterally and compromise the entire IT infrastructure.

PCI-ASV Scanning Datasheet
PCI DSS specifically requires that organizations undergo quarterly external vulnerability scans from an approved scanning vendor (ASV).CSW, an accredited ASV, performs vulnerability scans, evaluates the security of payment systems, and assesses Internet-facing systems.
Cyber Risk in Remote Desktop
Remote Desktops play a vital role in enabling employees to access office resources. Learn more on vulnerabilities tied to remote desktops and how to prevent them.
Cyber Risk in BI
Business intelligence (BI) helps you make tactical and strategic business decisions. In this report we have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in CRM
Gaining access to a company’s CRM lets someone gain key information like customer data, internal processes. We have analysed top CRM vendors, some of whom have both critical and high vulnerabilities.
Cyber Risk in Gateway
Attacking a gateway gives direct access to the entire data passed to an organization. We have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in Web Proxies
Our data threat analysis looks at some of the leading vendors from Gartner and Forrester’s research to present a bird’s eye view of the vulnerabilities in major web proxy vendors.
Cyber Risk in Database
As database management systems (DBMS) help in creating and managing databases, they become the primary targets for attackers to steal data through vulnerabilities. This report analyzes some of the leading vendors.
Cyber Risk in Enterprise Data Storage
Enterprise data storage provides a centralized server/drive as they create ease of access in handling data. As with all technologies Enterprise Data Storage has vulnerabilities that are exploited by attackers.

Cyber Risk in VPNs
We have analysed the vulnerabilities of some of the leading VPN vendors from Gartner and Forrester’s research. Learn more about VPNs and their vulnerabilities.
Cyber Risk in Online Conference
Online Conferencing is one of the key mediums through which users maintain communication to share and review their work. We select some of the leading vendors for our cyber risk analysis.
Cyber Risk in Working Remotely
Working form home leaves your work force vulnerable to threats. Learn how you can protect your remote workforce and their devices safe from cyber threats
.png)
AWS Cloud Security Assessment
CSW’s Cloud Security Assessment is designed to help you protect and optimize information, systems, data, and other assets hosted on AWS.
AWS Security as a Service
With our AWS Security as a Service offering, CSW becomes an extended member of your security team by continuously monitoring and assessing your AWS infrastructure.

AWS Cloud Security Management
CSW’s Cloud Security Management services are designed to continuously reduce your overall cloud attack surface by looking at your vulnerabilities across your entire technology stack.
SaaS Security Assessment
CSW's security assessment of Software-as-a-Service (SaaS) audits the software delivery model and resilience of the entire SaaS platform and all technology stacks involved—application, storage, and underlying infrastructure. We conduct a thorough analysis to help organizations remediate vulnerabilities that could compromise their SaaS platform.

API Penetration Testing
CSW’s API penetration test validates the security of your organizational methods and corresponding data ensuring that the transfer of information from web or mobile applications to other databases or systems can be safely carried out. Our testing methodology uses standardized processes to ensure consistency and ensure your API workflow is secure. We evaluate all applications based on OWASP API Top 10 and CWE Top 25 programming errors.
Web Application Penetration Testing
CSW’s web application penetration test provides a comprehensive understanding of how user inputs change data inside an application. Our proprietary framework helps to discover multiple attack vectors including thorough and dynamic testing of user, network and API interfaces.
Network Penetration Testing
CSW’s network penetration testing program provides clarity on critical vulnerabilities, helps organizations stay ahead of the attacker, aids in building a resilient security program to defend against advanced persistent threats (APTs) as well as attacker behavior, including tactics, techniques and procedures (TTPs) and assists you in maintaining a robust brand reputation.
Mobile Application Penetration Testing
The increasing demand for mobile applications worldwide multiplies the risk of a breach, especially when vulnerable applications are used to access sensitive data. CSW’s experienced penetration testers look for vulnerabilities in data storage, network communications (API), source codes, and security configurations during this engagement.
Internal Network Penetration Testing
We provide our clients with an accurate picture of the risk associated with their internally facing assets. Our Internal Network Penetration testing service is designed to test the effectiveness of an organization’s security controls towards preventing attackers from pivoting and moving laterally through your company’s infrastructure.
External Network Penetration Testing
We help our clients improve their security posture by providing guidance as to which weaknesses present the most risk to the business. This allows organizations to make more efficient use of their very limited resources by focusing on the most important issues.

Red Teaming Assessment
CSW's Red Teaming services emulate a real-world attack scenario in your organizational environment using any methods necessary to accomplish a pre-planned mission objective. Our red team closely mimics a real attacker’s tactics, techniques, and procedures (TTPs) to move stealthily across your attack surface.

Vulnerability Management as a Service
CSW’s security analysts will help you gain 360-degree visibility of your security exposure and help you remediate vulnerabilities that exist within your network.

Our Services & Solutions
CSW offers services such as Vulnerability Management as a Service (VMaaS), Penetration Testing (Network, Mobile, Cloud, SaaS, Web etc) and compliance services such as PCI ASV & DSS to improve your security posture and strengthen your defenses.
Ransomware Exposure Assessment
Ransomware Exposure Assessment helps identify vulnerabilities that are often targeted by threat actors to mount a ransomware attack on your organization.

Penetrating Testing Datasheet
Our penetration testing simulates a real-world attack on digital assets. We adopt a hacker’s perspective to detect and exploit vulnerabilities in an organization’s environment to determine if we can move laterally and compromise the entire IT infrastructure.

PCI-ASV Scanning Datasheet
PCI DSS specifically requires that organizations undergo quarterly external vulnerability scans from an approved scanning vendor (ASV).CSW, an accredited ASV, performs vulnerability scans, evaluates the security of payment systems, and assesses Internet-facing systems.

.png)
Ransomware Index Update Q2 & Q3 2022
The 2022 Index Update Q2 & Q3 report tracks the vulnerabilities that facilitate Ransomware attacks and delves deep into their MITRE ATT&CK tactics and techniques. The report also provides interesting observations about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022 and top ransomware vulnerabiltiies that could be exploited in the near future.
Ransomware Index Update Q1 2022
Ransomware Index Update for Q1 2022 dives deep into the latest developments in ransomware attack arsenal, and the gaps in data intelligence that act as a roadblock in organizations’ security journey.
.png)
Ransomware Spotlight Report 2022
The 2022 Spotlight report provides a deep insight into vulnerabilities that facilitate Ransomware attacks. Learn more about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022.
Ransomware Index Update Q3 2021
Ransomware Index Update for Q3 provides the latest ransomware trends, and the new groups, vulnerabilities and weaknesses tied to ransomware. Understand what vulnerabilities offer the greatest threat and stay protected.
Ransomware Index Update Q2 2021
Ransomware index update for Q2 looks at new vulnerabilities tied to ransomware, new exploits, APT Groups, and Ransomware families. Build resilience to defend your ecosystem from crippling ransomware attacks.
Ransomware Index Update Q1 2021
Ransomware index update for Q1 2021 brings new vulnerabilities, exploits, APT Groups and Ransomware families that have become active in the first quarter of 2021. Get updated insights about this evolving threat and know your exposure to it.
Ransomware 2021 Spotlight Report: Threat and Vulnerability Management
From APT groups, ransomware-as-a-service, targeted products and preferred weaknesses, this report delves deep into every aspect of ransomware and presents extensive insights and actionable information.
Cyber Risk in Remote Desktop
Remote Desktops play a vital role in enabling employees to access office resources. Learn more on vulnerabilities tied to remote desktops and how to prevent them.
Cyber Risk in BI
Business intelligence (BI) helps you make tactical and strategic business decisions. In this report we have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in CRM
Gaining access to a company’s CRM lets someone gain key information like customer data, internal processes. We have analysed top CRM vendors, some of whom have both critical and high vulnerabilities.
Cyber Risk in Gateway
Attacking a gateway gives direct access to the entire data passed to an organization. We have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in Web Proxies
Our data threat analysis looks at some of the leading vendors from Gartner and Forrester’s research to present a bird’s eye view of the vulnerabilities in major web proxy vendors.
Cyber Risk in Database
As database management systems (DBMS) help in creating and managing databases, they become the primary targets for attackers to steal data through vulnerabilities. This report analyzes some of the leading vendors.
Cyber Risk in Enterprise Data Storage
Enterprise data storage provides a centralized server/drive as they create ease of access in handling data. As with all technologies Enterprise Data Storage has vulnerabilities that are exploited by attackers.

Cyber Risk in VPNs
We have analysed the vulnerabilities of some of the leading VPN vendors from Gartner and Forrester’s research. Learn more about VPNs and their vulnerabilities.
Cyber Risk in Online Conference
Online Conferencing is one of the key mediums through which users maintain communication to share and review their work. We select some of the leading vendors for our cyber risk analysis.
Cyber Risk in Working Remotely
Working form home leaves your work force vulnerable to threats. Learn how you can protect your remote workforce and their devices safe from cyber threats
.png)
CSW Helps DreamSpring Migrate to AWS and Halve Hosting Costs
DreamSpring, a nonprofit community lender dedicated to eliminating systemic wealth inequities, partnered with CSW to migrate its lending platform to the Amazon Web Services (AWS) cloud computing platform.
How CSW Helped a Debt Recovery and Portfolio Management Company
Read about how CSW conducted a Red Teaming exercise on a leading American debt recovery and portfolio management company and helped them gain cyber resilience.
Decoding CISA KEV - KEV Metrics and Threat Associations
CSW and Securin experts took a deep dive into CISA KEVs to understand the risk that they pose to organizations. We analyzed each vulnerability to know their severity scores, exploitability, threat associations, weakness categories and impacted vendors and products etc.

Decoding CISA KEV - A Latency Analysis
CSW and Securin experts analyzed the latency of NVD, patch release, and scanner plugins in relation to the CISA KEV catalog to understand the exposures and windows of attack that make FCEB and Public Sector organizations vulnerable to crippling cyber attacks.

Decoding CISA KEV - MITRE Analysis
CSW and Securin experts mapped the entire CISA KEV catalog to MITRE’ AT&CK tactics and techniques and have prioritized the vulnerabilities with a complete kill chain. In this report, we take a deep dive into what makes these vulnerabilities extremely dangerous and why attackers go after them.
Decoding CISA KEV - Severity Scores & Weakness Analysis
CSW and Securin experts analyzed the severity scores of KEVs and used our proprietary risk score (Vulnerability Risk Score) to understand the true risk posed by each vulnerability. We also analyzed the Common Weakness Enumeration (CWE) of the vulnerabilities listed in the KEV catalog to understand what type of weakness category is contributing the most and why.
Decoding CISA KEV - Predictive Analysis & Early Warning
CSW and Securin experts red flag vulnerabilities that need to be part of the CISA KEV using Securin Vulnerability Intelligence (VI). Using its predictive scores, we provide recommendations about vulnerabilities that CISA needs to add to the KEV catalog.
.png)
Ransomware Index Update Q2 & Q3 2022
The 2022 Index Update Q2 & Q3 report tracks the vulnerabilities that facilitate Ransomware attacks and delves deep into their MITRE ATT&CK tactics and techniques. The report also provides interesting observations about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022 and top ransomware vulnerabiltiies that could be exploited in the near future.
.png)
CSW Helps DreamSpring Migrate to AWS and Halve Hosting Costs
DreamSpring, a nonprofit community lender dedicated to eliminating systemic wealth inequities, partnered with CSW to migrate its lending platform to the Amazon Web Services (AWS) cloud computing platform.
Ransomware Index Update Q1 2022
Ransomware Index Update for Q1 2022 dives deep into the latest developments in ransomware attack arsenal, and the gaps in data intelligence that act as a roadblock in organizations’ security journey.
.png)
AWS Cloud Security Assessment
CSW’s Cloud Security Assessment is designed to help you protect and optimize information, systems, data, and other assets hosted on AWS.
AWS Security as a Service
With our AWS Security as a Service offering, CSW becomes an extended member of your security team by continuously monitoring and assessing your AWS infrastructure.

AWS Cloud Security Management
CSW’s Cloud Security Management services are designed to continuously reduce your overall cloud attack surface by looking at your vulnerabilities across your entire technology stack.
SaaS Security Assessment
CSW's security assessment of Software-as-a-Service (SaaS) audits the software delivery model and resilience of the entire SaaS platform and all technology stacks involved—application, storage, and underlying infrastructure. We conduct a thorough analysis to help organizations remediate vulnerabilities that could compromise their SaaS platform.

API Penetration Testing
CSW’s API penetration test validates the security of your organizational methods and corresponding data ensuring that the transfer of information from web or mobile applications to other databases or systems can be safely carried out. Our testing methodology uses standardized processes to ensure consistency and ensure your API workflow is secure. We evaluate all applications based on OWASP API Top 10 and CWE Top 25 programming errors.
.png)
Ransomware Spotlight Report 2022
The 2022 Spotlight report provides a deep insight into vulnerabilities that facilitate Ransomware attacks. Learn more about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022.
Ransomware Index Update Q3 2021
Ransomware Index Update for Q3 provides the latest ransomware trends, and the new groups, vulnerabilities and weaknesses tied to ransomware. Understand what vulnerabilities offer the greatest threat and stay protected.
Web Application Penetration Testing
CSW’s web application penetration test provides a comprehensive understanding of how user inputs change data inside an application. Our proprietary framework helps to discover multiple attack vectors including thorough and dynamic testing of user, network and API interfaces.
Network Penetration Testing
CSW’s network penetration testing program provides clarity on critical vulnerabilities, helps organizations stay ahead of the attacker, aids in building a resilient security program to defend against advanced persistent threats (APTs) as well as attacker behavior, including tactics, techniques and procedures (TTPs) and assists you in maintaining a robust brand reputation.
Mobile Application Penetration Testing
The increasing demand for mobile applications worldwide multiplies the risk of a breach, especially when vulnerable applications are used to access sensitive data. CSW’s experienced penetration testers look for vulnerabilities in data storage, network communications (API), source codes, and security configurations during this engagement.
Internal Network Penetration Testing
We provide our clients with an accurate picture of the risk associated with their internally facing assets. Our Internal Network Penetration testing service is designed to test the effectiveness of an organization’s security controls towards preventing attackers from pivoting and moving laterally through your company’s infrastructure.
External Network Penetration Testing
We help our clients improve their security posture by providing guidance as to which weaknesses present the most risk to the business. This allows organizations to make more efficient use of their very limited resources by focusing on the most important issues.

Red Teaming Assessment
CSW's Red Teaming services emulate a real-world attack scenario in your organizational environment using any methods necessary to accomplish a pre-planned mission objective. Our red team closely mimics a real attacker’s tactics, techniques, and procedures (TTPs) to move stealthily across your attack surface.

Vulnerability Management as a Service
CSW’s security analysts will help you gain 360-degree visibility of your security exposure and help you remediate vulnerabilities that exist within your network.
How CSW Helped a Debt Recovery and Portfolio Management Company
Read about how CSW conducted a Red Teaming exercise on a leading American debt recovery and portfolio management company and helped them gain cyber resilience.
Ransomware Index Update Q2 2021
Ransomware index update for Q2 looks at new vulnerabilities tied to ransomware, new exploits, APT Groups, and Ransomware families. Build resilience to defend your ecosystem from crippling ransomware attacks.
Ransomware Index Update Q1 2021
Ransomware index update for Q1 2021 brings new vulnerabilities, exploits, APT Groups and Ransomware families that have become active in the first quarter of 2021. Get updated insights about this evolving threat and know your exposure to it.

Our Services & Solutions
CSW offers services such as Vulnerability Management as a Service (VMaaS), Penetration Testing (Network, Mobile, Cloud, SaaS, Web etc) and compliance services such as PCI ASV & DSS to improve your security posture and strengthen your defenses.
Ransomware 2021 Spotlight Report: Threat and Vulnerability Management
From APT groups, ransomware-as-a-service, targeted products and preferred weaknesses, this report delves deep into every aspect of ransomware and presents extensive insights and actionable information.
Ransomware Exposure Assessment
Ransomware Exposure Assessment helps identify vulnerabilities that are often targeted by threat actors to mount a ransomware attack on your organization.

Penetrating Testing Datasheet
Our penetration testing simulates a real-world attack on digital assets. We adopt a hacker’s perspective to detect and exploit vulnerabilities in an organization’s environment to determine if we can move laterally and compromise the entire IT infrastructure.

PCI-ASV Scanning Datasheet
PCI DSS specifically requires that organizations undergo quarterly external vulnerability scans from an approved scanning vendor (ASV).CSW, an accredited ASV, performs vulnerability scans, evaluates the security of payment systems, and assesses Internet-facing systems.
Cyber Risk in Remote Desktop
Remote Desktops play a vital role in enabling employees to access office resources. Learn more on vulnerabilities tied to remote desktops and how to prevent them.
Cyber Risk in BI
Business intelligence (BI) helps you make tactical and strategic business decisions. In this report we have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in CRM
Gaining access to a company’s CRM lets someone gain key information like customer data, internal processes. We have analysed top CRM vendors, some of whom have both critical and high vulnerabilities.
Cyber Risk in Gateway
Attacking a gateway gives direct access to the entire data passed to an organization. We have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in Web Proxies
Our data threat analysis looks at some of the leading vendors from Gartner and Forrester’s research to present a bird’s eye view of the vulnerabilities in major web proxy vendors.
Cyber Risk in Database
As database management systems (DBMS) help in creating and managing databases, they become the primary targets for attackers to steal data through vulnerabilities. This report analyzes some of the leading vendors.
Cyber Risk in Enterprise Data Storage
Enterprise data storage provides a centralized server/drive as they create ease of access in handling data. As with all technologies Enterprise Data Storage has vulnerabilities that are exploited by attackers.

Cyber Risk in VPNs
We have analysed the vulnerabilities of some of the leading VPN vendors from Gartner and Forrester’s research. Learn more about VPNs and their vulnerabilities.
Cyber Risk in Online Conference
Online Conferencing is one of the key mediums through which users maintain communication to share and review their work. We select some of the leading vendors for our cyber risk analysis.
Cyber Risk in Working Remotely
Working form home leaves your work force vulnerable to threats. Learn how you can protect your remote workforce and their devices safe from cyber threats
.png)
Ransomware Index Update Q2 & Q3 2022
The 2022 Index Update Q2 & Q3 report tracks the vulnerabilities that facilitate Ransomware attacks and delves deep into their MITRE ATT&CK tactics and techniques. The report also provides interesting observations about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022 and top ransomware vulnerabiltiies that could be exploited in the near future.
Ransomware Index Update Q1 2022
Ransomware Index Update for Q1 2022 dives deep into the latest developments in ransomware attack arsenal, and the gaps in data intelligence that act as a roadblock in organizations’ security journey.
.png)
Ransomware Spotlight Report 2022
The 2022 Spotlight report provides a deep insight into vulnerabilities that facilitate Ransomware attacks. Learn more about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022.
Ransomware Index Update Q3 2021
Ransomware Index Update for Q3 provides the latest ransomware trends, and the new groups, vulnerabilities and weaknesses tied to ransomware. Understand what vulnerabilities offer the greatest threat and stay protected.
Ransomware Index Update Q2 2021
Ransomware index update for Q2 looks at new vulnerabilities tied to ransomware, new exploits, APT Groups, and Ransomware families. Build resilience to defend your ecosystem from crippling ransomware attacks.
Ransomware Index Update Q1 2021
Ransomware index update for Q1 2021 brings new vulnerabilities, exploits, APT Groups and Ransomware families that have become active in the first quarter of 2021. Get updated insights about this evolving threat and know your exposure to it.
Ransomware 2021 Spotlight Report: Threat and Vulnerability Management
From APT groups, ransomware-as-a-service, targeted products and preferred weaknesses, this report delves deep into every aspect of ransomware and presents extensive insights and actionable information.
Cyber Risk in Remote Desktop
Remote Desktops play a vital role in enabling employees to access office resources. Learn more on vulnerabilities tied to remote desktops and how to prevent them.
Cyber Risk in BI
Business intelligence (BI) helps you make tactical and strategic business decisions. In this report we have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in CRM
Gaining access to a company’s CRM lets someone gain key information like customer data, internal processes. We have analysed top CRM vendors, some of whom have both critical and high vulnerabilities.
Cyber Risk in Gateway
Attacking a gateway gives direct access to the entire data passed to an organization. We have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in Web Proxies
Our data threat analysis looks at some of the leading vendors from Gartner and Forrester’s research to present a bird’s eye view of the vulnerabilities in major web proxy vendors.
Cyber Risk in Database
As database management systems (DBMS) help in creating and managing databases, they become the primary targets for attackers to steal data through vulnerabilities. This report analyzes some of the leading vendors.
Cyber Risk in Enterprise Data Storage
Enterprise data storage provides a centralized server/drive as they create ease of access in handling data. As with all technologies Enterprise Data Storage has vulnerabilities that are exploited by attackers.

Cyber Risk in VPNs
We have analysed the vulnerabilities of some of the leading VPN vendors from Gartner and Forrester’s research. Learn more about VPNs and their vulnerabilities.
Cyber Risk in Online Conference
Online Conferencing is one of the key mediums through which users maintain communication to share and review their work. We select some of the leading vendors for our cyber risk analysis.
Cyber Risk in Working Remotely
Working form home leaves your work force vulnerable to threats. Learn how you can protect your remote workforce and their devices safe from cyber threats
.png)
Ransomware Index Update Q2 & Q3 2022
The 2022 Index Update Q2 & Q3 report tracks the vulnerabilities that facilitate Ransomware attacks and delves deep into their MITRE ATT&CK tactics and techniques. The report also provides interesting observations about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022 and top ransomware vulnerabiltiies that could be exploited in the near future.
Ransomware Index Update Q1 2022
Ransomware Index Update for Q1 2022 dives deep into the latest developments in ransomware attack arsenal, and the gaps in data intelligence that act as a roadblock in organizations’ security journey.
.png)
Ransomware Spotlight Report 2022
The 2022 Spotlight report provides a deep insight into vulnerabilities that facilitate Ransomware attacks. Learn more about Ransomware Families, APT Groups, Attack Trends and Predictions for 2022.
Ransomware Index Update Q3 2021
Ransomware Index Update for Q3 provides the latest ransomware trends, and the new groups, vulnerabilities and weaknesses tied to ransomware. Understand what vulnerabilities offer the greatest threat and stay protected.
Ransomware Index Update Q2 2021
Ransomware index update for Q2 looks at new vulnerabilities tied to ransomware, new exploits, APT Groups, and Ransomware families. Build resilience to defend your ecosystem from crippling ransomware attacks.
Ransomware Index Update Q1 2021
Ransomware index update for Q1 2021 brings new vulnerabilities, exploits, APT Groups and Ransomware families that have become active in the first quarter of 2021. Get updated insights about this evolving threat and know your exposure to it.
Ransomware 2021 Spotlight Report: Threat and Vulnerability Management
From APT groups, ransomware-as-a-service, targeted products and preferred weaknesses, this report delves deep into every aspect of ransomware and presents extensive insights and actionable information.
Cyber Risk in Remote Desktop
Remote Desktops play a vital role in enabling employees to access office resources. Learn more on vulnerabilities tied to remote desktops and how to prevent them.
Cyber Risk in BI
Business intelligence (BI) helps you make tactical and strategic business decisions. In this report we have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in CRM
Gaining access to a company’s CRM lets someone gain key information like customer data, internal processes. We have analysed top CRM vendors, some of whom have both critical and high vulnerabilities.
Cyber Risk in Gateway
Attacking a gateway gives direct access to the entire data passed to an organization. We have selected some of the leading vendors from Gartner and Forrester’s research and analysed their vulnerabilities.
Cyber Risk in Web Proxies
Our data threat analysis looks at some of the leading vendors from Gartner and Forrester’s research to present a bird’s eye view of the vulnerabilities in major web proxy vendors.
Cyber Risk in Database
As database management systems (DBMS) help in creating and managing databases, they become the primary targets for attackers to steal data through vulnerabilities. This report analyzes some of the leading vendors.
Cyber Risk in Enterprise Data Storage
Enterprise data storage provides a centralized server/drive as they create ease of access in handling data. As with all technologies Enterprise Data Storage has vulnerabilities that are exploited by attackers.

Cyber Risk in VPNs
We have analysed the vulnerabilities of some of the leading VPN vendors from Gartner and Forrester’s research. Learn more about VPNs and their vulnerabilities.
Cyber Risk in Online Conference
Online Conferencing is one of the key mediums through which users maintain communication to share and review their work. We select some of the leading vendors for our cyber risk analysis.
Cyber Risk in Working Remotely
Working form home leaves your work force vulnerable to threats. Learn how you can protect your remote workforce and their devices safe from cyber threats
.png)
CSW Helps DreamSpring Migrate to AWS and Halve Hosting Costs
DreamSpring, a nonprofit community lender dedicated to eliminating systemic wealth inequities, partnered with CSW to migrate its lending platform to the Amazon Web Services (AWS) cloud computing platform.
How CSW Helped a Debt Recovery and Portfolio Management Company
Read about how CSW conducted a Red Teaming exercise on a leading American debt recovery and portfolio management company and helped them gain cyber resilience.